Most cybersecurity strategies are built on a lie: the belief that a wall is enough to keep an empire safe. We build firewalls and VPNs like modern-day Hadrian’s Walls—long, expensive, and ultimately thin lines of defense. When those lines feel too thin, we hire digital sentries to watch them, pouring millions into detection.
But history shows us that thin lines eventually break, and by the time a sentry sounds the alarm, the city is already being sacked. Detection is not protection.
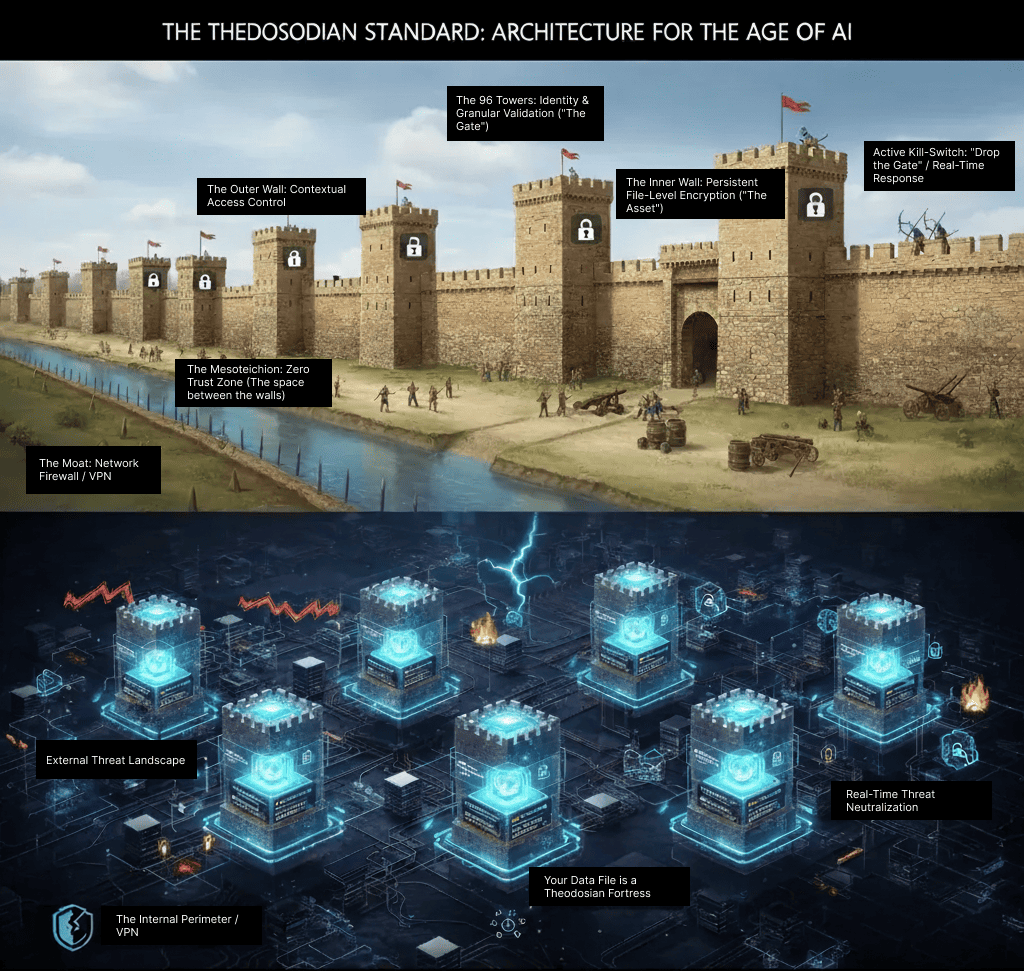
If you want to protect what matters, you don't look to the Roman borders; you look to the Theodosiana Walls of Constantinople. They didn't just provide a barrier or a better lookout; they provided a multi-layered architecture that collapsed the perimeter directly onto the asset. It was a data-centric strategy that survived the impossible for over a millennium. They didn't just watch for threats; they made the impact of those threats irrelevant.
1. The Death of the "Single Line" Defense
Hadrian’s Wall was a single point of failure. If you scaled it, the province was yours. Most modern IT stacks are built the same way: once an attacker bypasses the firewall, they have "lateral movement" across the entire network.
The Theodosiana approach was different. It utilized Defense in Depth:
- The Moat: The first barrier to slow the enemy down (Firewalls/VPNs).
- The Outer Wall: A secondary tier that filters and inspects the threat (Contextual traffic filtering and DLP).
- The Inner Wall: The massive, final layer of protection that actually holds the asset (The encrypted file).
Most importantly, our architecture doesn't just watch; it acts. Every time someone tries to enter a "Tower" (access a file), we perform granular identity and behavioral checks. If the person isn't who they say they are, or if they start acting maliciously, we "drop the gate," severing access before a single byte is compromised.
🔐 Stop Defending the Border; Start Fortifying the Asset!
Discover how Theodosiana applies the principles of 'Defense in Depth' to every individual file in your network.
2. Segmented Sovereignty: The 96 Towers
The genius of the Theodosiana system was its decentralized defense. The wall was punctuated by 96 massive towers. Crucially, these towers were built as independent structures. If one tower was damaged or captured, the defenders could seal it off without compromising the rest of the wall.
🛡️ Old Security: A single gatekeeper at the city's main entrance. If they are tricked, the entire city falls.
🛡️ Theodosiana Security: Every file is its own Tower. Each Tower acts as an independent gatehouse where identity & granular validation occur. Even if an attacker reaches the Inner Wall, they cannot pass through to the data unless they satisfy the real-time compliance checks at the gate. If they fail, we "drop the gate," severing access instantly while the rest of the "City" remains unaware and secure.
3. The Lookout Paradox (Why Detection Isn’t Enough)
Modern security teams spend millions on detection tools, the digital equivalent of Byzantine sentries. But a sentry can only watch as the city is sacked. If your security strategy relies on "detecting" a breach to trigger a response, you are already too late.
At Theodosiana, we move the focus from detecting the threat to neutralizing its impact. By the time a detection tool flags an anomaly, our file-level encryption has already ensured there is nothing for the attacker to read. We don't just watch the breach; we make the breach irrelevant.
4. Persistent Protection (The "Gatekeeper" Myth)
The Theodosiana Walls didn't just work when the Emperor was watching; they worked because they were structurally designed to be a permanent deterrent. They didn't rely on a single gatekeeper being awake; the architecture itself was the security.
5. The "Fifth Column": Guarding the Interior
History tells us that many fortresses fell not to sieges, but to someone opening a side door from the inside. Whether through betrayal or simple human error, the internal threat is always present.
6. Preparing for the "Gunpowder Moment"
For 1,000 years, the Walls were invincible. They only fell in 1453 because the Ottomans brought a new, "zero-day" technology: the Great Cannon.
🛡️ Theodosiana doesn't just sit there; it performs active checks every time a file is accessed.
🛡️ It verifies location, device, and user identity in real-time and more.
🛡️ It is security built for the "Gunpowder Age" of cyber warfare.
Five Key Takeaways for Security Leaders
The Theodosiana Walls didn't just survive on luck; they survived on a philosophy of active resilience.
To apply the "Theodosiana Standard" to your organization, focus on these five shifts:
- Prioritize "Micro-Fortresses" over Perimeters: Stop spending 80% of your budget on the network edge. Shift your investment to the Inner Wall (per-file encryption) and the Towers (granular identity gates). This ensures that even when the network is porous, your data remains an impregnable fortress.
- Adopt Discretized Defense: Ensure that a single compromised credential doesn't grant "keys to the city." By using independent encryption and unique access checks for every file, you contain breaches at the source and prevent lateral movement.
- Shift from Detection to Prevention: Stop relying on lookouts to tell you when you’ve been robbed. Detection tells you the damage is done; architecture prevents the damage from happening. Invest in systems that protect data by default, so you aren't racing against a stopwatch to stop an exfiltration in progress.
- Move from Static to Active Compliance: A "wall" that doesn't react is just a target. Your security should perform Active Validation (checking device, user location, and behavioral intent) every time data is accessed, not just once a year during an audit/assessment.
- Prepare for the "Gunpowder Moment": Traditional encryption and perimeter tools will eventually be outpaced by AI-driven attacks. Building an architecture of Defense in Depth is the only way to ensure your organization remains "impregnable" for the long haul.
Constructing an Active Fortress
The Romans didn't keep Constantinople safe for a millennium by filling out compliance checklists; they did it through superior architecture. At Theodosiana, we believe data security should be an architectural certainty, not a peripheral afterthought.
We don't just build walls; we turn your data into a fortress that can withstand the sieges of the 21st century.
🔐 Is Your Data an Open City or a Theodosiana Fortress?
In an age of 'Gunpowder' threats, passive compliance isn't enough. Build your defense on a foundation of persistent, per-file encryption.
FAQs: The Last Great Empire and Data-Centric Security
What is the difference between perimeter security and data-centric security?
Perimeter security (like Hadrian’s Wall) focuses on keeping attackers out of a network using firewalls and VPNs. Once the perimeter is breached, the data inside is often unprotected. Data-centric security (The Theodosiana model) assumes the perimeter will eventually fail and instead embeds protection—such as encryption and access policies—directly into the individual files themselves.
Why are the Theodosiana Walls a better model for cybersecurity than other historical defenses?
Most historical walls were "single-line" defenses that were easily bypassed. The Theodosiana Walls used Defense in Depth, featuring three distinct layers of protection and 96 independent towers. In cybersecurity, this translates to a multi-layered strategy where every file is an independent fortress, ensuring that a single breach does not lead to a total system failure.
How does file-level encryption protect against "Insider Threats"?
Traditional security often trusts anyone who is already "inside the city gates." File-level encryption follows a Zero Trust philosophy. Even if an attacker steals an employee's credentials or a disgruntled insider attempts to exfiltrate data, they cannot read the files without specific, real-time decryption keys that are validated against a rigorous set of security parameters.
What is a "Gunpowder Moment" in cybersecurity?
A "Gunpowder Moment" refers to the arrival of a new technology that renders traditional defenses obsolete, much like how cannons eventually brought down the Theodosiana Walls. In the modern era, these "cannons" include AI-driven phishing, quantum computing, and sophisticated supply chain attacks. A data-centric architecture is designed to remain resilient even when these new threats shatter the traditional network perimeter.
